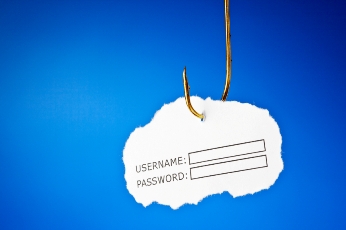
Eeek. How did this happen? Did the website get hacked? We did a scan of the server, checked the logs, and rechecked the intrusion detection service logs. No breach. So how did this happen? Turns out that the association publishes a full staff list and it would have been easy for anyone to find the email addresses of a senior VP and an admin. It’s not hard to create an email address and “hide” the email by displaying the “pretty name” in the email header. BTW, turns out a number of our clients are getting these types of emails.
Here’s another scenario that will scare you. Several clients have reported that their exhibitors are receiving calls from people posing as the association staff exhibitor contact. The caller goes on to ask if the exhibitor has booked a hotel room. If the exhibitor says no, the caller asks for a credit card and bam, the credit card has now been breached.
Eeek and double eeek. These types of attacks are called social engineering attacks. Wikipedia defines “social engineering. in the context of information security, refers to psychological manipulation of people into performing actions or divulging confidential information. The attacks described above are not technical threats, they are human threats and they are on the rise.
So how do you protect your organization? I could spend days talking about social engineering, but here are my top tips:
- Talk to your staff about social engineering: what it is, the dangers, what it looks like.
- Train your staff to be suspicious. One IT Director I spoke with said, “I’ve trained my staff to be paranoid. If they get a request that looks fishy, they need to confirm the request by voice. And they are told that senior staff NEVER ask for exports and reports from the database via email.”
- Train your staff to never divulge passwords, account numbers or other confidential information over the phone or email unless they can verify the request in person or via voice.
- If a social engineering attack occurs, don’t sweep it under the rug and pretend it didn’t happen. Talk about it, train on it, discuss it.
- Talk to your IT vendors about training for your staff.
- Keep reading and educating yourself and your staff about social engineering.
How about you? Has your organization been victimized by a social engineering hack? What are YOU doing to protect yourself and your organization?